Tools Covered in this Course
Course Details
Course Overview:
The EC Council CPENT course is a highly beneficial penetration testing program that will help you establish yourself as an elite pentester in the cybersecurity industry and take your career to new heights. In the CPENT course, you will learn the usage of various advanced penetration testing methodologies, techniques, and tools that will strengthen your profile and enhance your value as a highly demanded penetration tester. To ice the cake, you will get the chance of earning two certificates with a single CPENT certification cost.
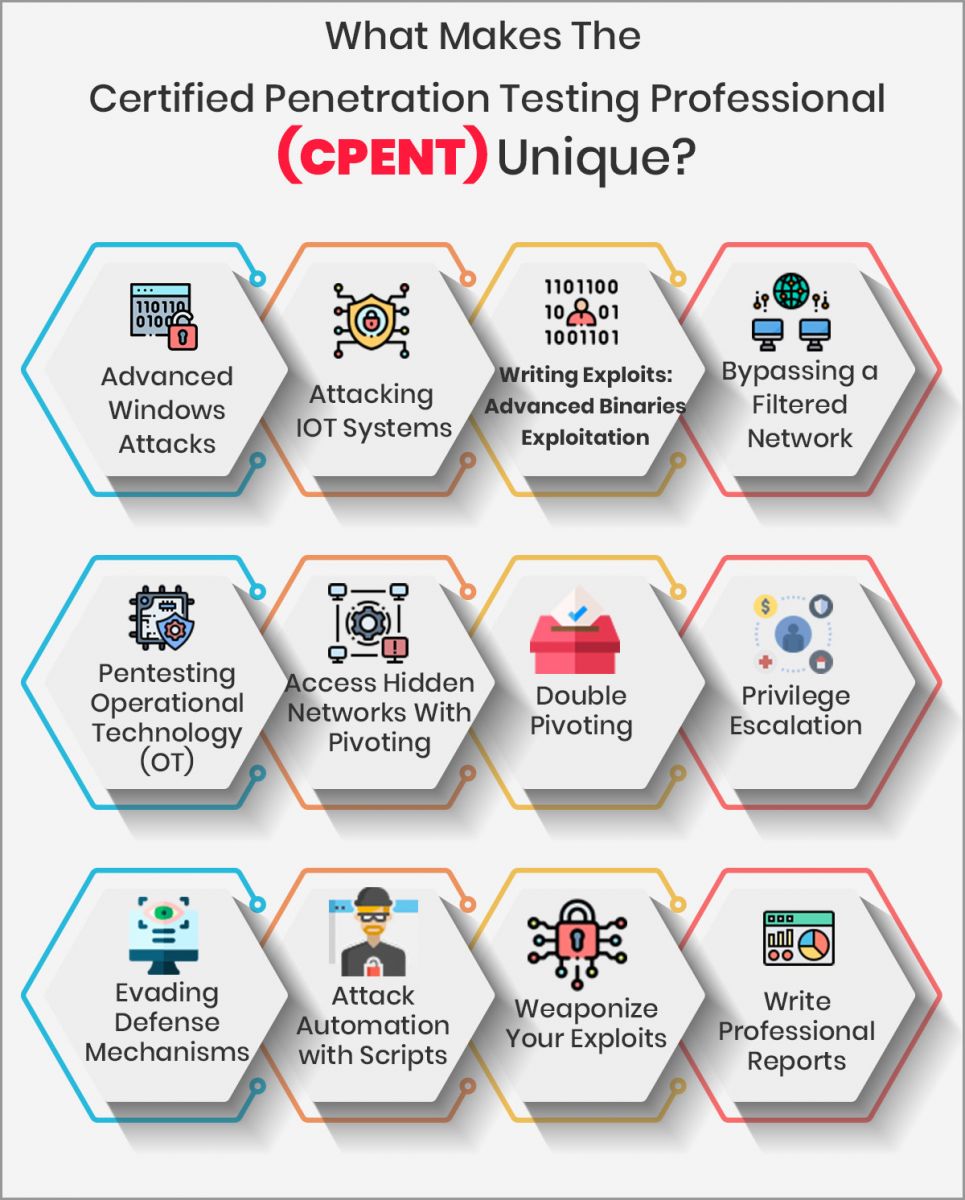
WHAT YOU WILL LEARN IN CPENT TRAINING COURSE?
The I-Medita Certified Penetration Tester Training Course offers a perfect mix of manual and automated penetration testing techniques. The objective of the course is to equip you with the knowledge & skills required to overcome the most advanced obstacles faced by real-world penetration testers. During the Certified Penetration Tester Training, you will gain in-depth knowledge of:
- Advanced Windows Attacks
- Attacking IoT Systems
- Writing Exploits: Advanced Binary Exploitation
- Bypassing a Filtered Network
- Pen testing Operational Technology (OT)
- Access Hidden Networks with Pivoting
- Double Pivoting
- Privilege Escalation
- Evading Defense Mechanisms
- Attack Automation with Scripts
- Weaponize Your Exploits
- Write Professional Reports
CPENT Target Candidates will be:
- Ethical Hackers
- Penetration Testers
- Network server administrators
- Firewall Administrators
- Security Testers
- System Administrators and Risk Assessment professionals
- CPENT Maps to the following Industry Job Roles:
- Cyber Security Forensic Analyst
- Cyber Threat Analyst Tier 2
- Cyber Threat Intelligence Analyst
- Information Security Analyst
- Cyber Security Engineer
- Application Security Analyst II
- Cyber Security Assurance Engineer
- Senior Information Assurance/ Security Specialist
- Security Systems Analyst
- Security Operations Center (SOC) Analyst
What’s Different?
Advanced Windows Attacks: The challenge aims to test the knowledge of PowerShell of the candidate, where the latter is required to use PowerShell bypass techniques along with other methods to gain access to a windows machine that has defenses in place.
Attacking IoT Systems: CPENT is the first certification to introduce hacking IoT devices that starts with searching the device, gaining access, identifying firmware, extraction, and performing reverse engineering.
Advanced Binaries Exploitation: Penetration testers are required to gain access to the system and look for flawed binaries, use reverse engineering, and write exploits for privilege escalation.
Bypassing a Filtered Network: In a segmented architecture, the challenger has to identify the filtering of the architecture then leverage this to gain access to the web applications by compromising it and then extract the required data
Pentesting Operational Technology (OT): The challenge is again a first of its kind in a penetration testing certification. The tester has to gain access to a dedicated OT network and perform modifications in the existing data by penetrating from the IT network side.
Access Hidden Networks With Pivoting: Tester has to penetrate into the direct network by identifying the filtering rules and then attempt pivots, through a filter, into the hidden network using single pivoting methods.
Double Pivoting: Quoting EC-Council “CPENT is the first certification in the world that requires you to access hidden networks using double pivoting.” This challenge tests the skills of the tester as the pivot has to be set up manually.
Attack Automation with Scripts: The challenge requires the tester to use advanced penetration techniques and scripting using languages like Perl, Python, Ruby, PowerShell, BASH, and use techniques like Metasploit and Fuzzing techniques.
Weaponize Your Exploits: This provides a chance to the testers to use their coding skills, carry their own tools to complete the challenge.
Apart from these, the challenges also require the testers to evade various defense mechanisms, use the latest methods for privilege escalation and summarize everything in a report that, in the real world, could be presented to the client/higher management to take vital business decisions.
CPENT Course Outline
-
Module 01: Introduction to Penetration Testing
-
Module 02: Penetration Testing Scoping and Engagement
-
Module 03: Open Source Intelligence (OSINT)
-
Module 04: Social Engineering Penetration Testing
-
Module 05: Network Penetration Testing – External
-
Module 06: Network Penetration Testing– Internal
-
Module 07: Network Penetration Testing – Perimeter Devices
-
Module 08: Web Application Penetration Testing
-
Module 09: Wireless Penetration Testing
-
Module 10: IoT Penetration Testing
-
Module 11: OT/SCADA Penetration Testing
-
Module 12: Cloud Penetration Testing
-
Module 13: Binary Analysis and Exploitation
-
Module 14: Report Writing and Post Testing Actions
Pre-Requisite
CPENT certification Course Needs:
Extensive knowledge of penetration testing across multiple disciplines extending from windows, IoTs, inline defenses to automation, operational technology, and advanced skills in binary exploitation. The certification tests the knowledge of tester not only on automated tools but manual testing skills as well.
Exam Info
CPENT is an entirely practical exam which is conducted online and is proctored remotely. The exam duration is 24 hours. The candidates have two options to proceed with the exam. They can either take the exam in one go, i.e., 24 hours straight, or go for 2-12 hour exams. Candidates are required to submit their penetration testing reports within 7 days post the completion of the exam.
